Most companies still think quantum threats are a future problem. That assumption is becoming more dangerous every year. Because the biggest issue is not that quantum computers will break encryption tomorrow morning. The bigger issue is that attackers do not need to wait for quantum capability to become mainstream before the threat becomes real.
They can steal encrypted data today, store it quietly, and decrypt it later once quantum systems become capable enough. That strategy already has a name. Harvest Now, Decrypt Later.
And if your organization stores customer records, financial information, healthcare data, intellectual property, regulated documents, internal communications, or long-retention business records, then this is not theoretical anymore. It is a strategic security problem that already affects your long-term risk posture.
That is why Post-Quantum Cryptography is becoming one of the most important cybersecurity priorities for forward-looking enterprises.
Why This Threat Matters More Than Most Organizations Realize
Traditional public-key cryptography was built around mathematical problems that classical computers struggle to solve efficiently. Quantum computers change that equation.
Algorithms like RSA, ECC, and Diffie-Hellman could become vulnerable once sufficiently powerful quantum systems emerge. That means a huge percentage of modern digital infrastructure may eventually require replacement.
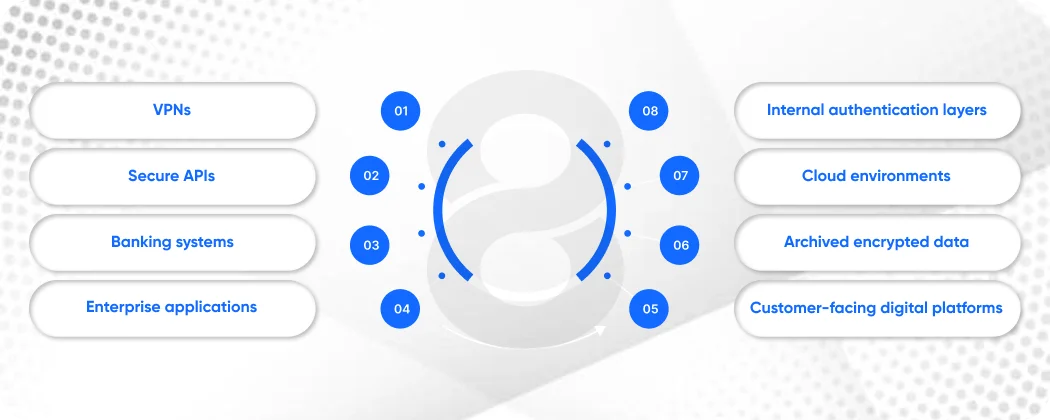
This affects:
- VPNs
- Secure APIs
- Banking systems
- Enterprise applications
- Internal authentication layers
- Cloud environments
- Archived encrypted data
- Customer-facing digital platforms
And because migration takes years in large organizations, preparation cannot start when the threat arrives. It has to start before. That is where Post-Quantum Cryptography migration becomes less of a technical upgrade and more of a strategic infrastructure initiative.
What Is Post-Quantum Cryptography?
Post-Quantum Cryptography refers to cryptographic algorithms designed to remain secure against attacks from both classical and quantum computers. These algorithms are specifically built to replace vulnerable public-key systems while maintaining usability across modern software and infrastructure environments.
Unlike quantum cryptography, which requires specialized hardware, PQC can typically be implemented through software and infrastructure upgrades. That makes it practical. But practical does not mean simple. Because replacing cryptography across enterprise systems is rarely straightforward.
Read More: 10 Best Open-Source Large Language Models for Your Next Venture
Why Most Organizations Underestimate PQC Migration Complexity
Leadership often hears “replace encryption” and imagines a contained technical project. It is not. Cryptography is buried inside far more systems than most organizations realize. It exists inside:
Hidden Dependency Area |
Common Examples |
| Application Security | Login systems, APIs, session management |
| Infrastructure | VPNs, TLS certificates, networking |
| Data Protection | Database encryption, backups, archives |
| Devices | IoT hardware, manufacturing systems, mobile devices |
| Vendor Platforms | SaaS tools, third-party integrations |
The challenge is not choosing new algorithms. The challenge is discovering where cryptography exists in the first place.
Read More: GreenOps Blueprint for Sustainable AI Infrastructure
The 10-Step Roadmap for PQC Migration
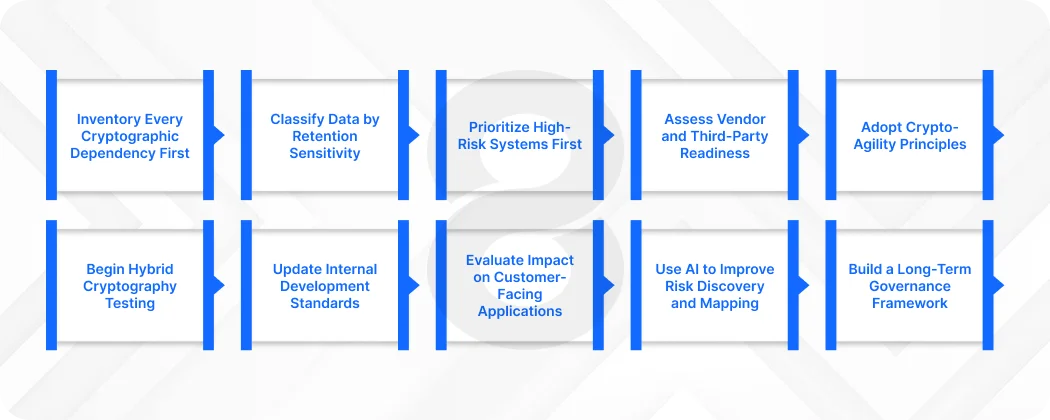
1. Inventory Every Cryptographic Dependency First
You cannot migrate what you have not mapped. Most enterprises underestimate how many systems rely on vulnerable cryptography. That includes older internal tools, forgotten APIs, vendor software, archived backups, and authentication services.
Start by identifying:
- All encryption protocols in use
- Certificate management systems
- Public-key infrastructure dependencies
- Legacy applications using RSA/ECC
- Long-term encrypted archives
- Third-party vendor cryptographic dependencies
Without this inventory, migration planning becomes guesswork.
2. Classify Data by Retention Sensitivity
Not all data needs quantum-resistant protection immediately. The priority is protecting data that will still be valuable years from now.
Examples include:
- Healthcare records
- Financial documents
- Government data
- Intellectual property
- Legal records
- Enterprise trade secrets
If the data must remain confidential for 5–20+ years, it is already exposed to harvest-now-decrypt-later risk. This is where Post-Quantum Cryptography planning becomes urgent.
3. Prioritize High-Risk Systems First
Trying to migrate everything simultaneously creates chaos. Prioritize systems based on:
- Data sensitivity
- Exposure level
- Regulatory pressure
- Replacement complexity
- Business criticality
A phased approach usually works better than full replacement.
4. Assess Vendor and Third-Party Readiness
Many businesses rely heavily on external platforms. That creates dependency risk.
Ask vendors:
- Do they have PQC migration roadmaps?
- Are their APIs quantum-ready?
- What standards are they adopting?
- What migration timeline are they targeting?
Your internal readiness means little if vendors lag behind.
5. Adopt Crypto-Agility Principles
One of the smartest things organizations can do is stop hardcoding cryptographic assumptions into infrastructure. Crypto-agility means designing systems so algorithms can be swapped later without major rebuilds.
Crypto-agility should influence future:
- Software development architecture
- API design
- Authentication frameworks
- Security infrastructure planning
6. Begin Hybrid Cryptography Testing
Many enterprises are testing hybrid models during transition periods. Hybrid cryptography combines:
- Traditional algorithms
- Quantum-resistant algorithms
This allows organizations to maintain compatibility while gradually introducing stronger protections. It is often the most practical transitional strategy.
7. Update Internal Development Standards
Security modernization must influence engineering practices. Development teams should begin incorporating PQC-readiness into:
- Internal coding standards
- Secure architecture policies
- API security frameworks
- Encryption implementation guidelines
This affects future software development decisions directly. Because building new systems on old cryptographic assumptions only creates future rework.
8. Evaluate Impact on Customer-Facing Applications
Migration affects external products too. Quantum-resistant protocols may impact:
- Performance
- Certificate sizes
- Network overhead
- Authentication flow design
That matters for:
- Mobile app development environments
- Customer portals
- Enterprise dashboards
- Web platforms
Security changes that hurt usability create adoption friction. Planning must balance both.
9. Use AI to Improve Risk Discovery and Mapping
Large enterprises often struggle to manually locate every cryptographic dependency. That is where AI development can assist.
AI-based analysis tools can help identify:
- Hidden cryptographic implementations
- Codebase vulnerabilities
- Legacy encryption dependencies
- Infrastructure mapping gaps
Advanced AI integration also helps prioritize remediation based on risk modeling. Used correctly, AI speeds up discovery significantly.
10. Build a Long-Term Governance Framework
Migration is not a one-time project. It becomes part of ongoing security governance.
Your organization needs:
- PQC review policies
- Vendor compliance standards
- Upgrade schedules
- Audit frameworks
- Continuous cryptographic monitoring
Because Post-Quantum Cryptography is not just a migration. It is an infrastructure evolution.
Common Mistakes That Quietly Derail PQC Projects

Even organizations that take quantum risk seriously often make preventable mistakes. The most common mistakes include:
Treating It Like a Pure IT Project
PQC affects risk, compliance, architecture, vendors, and product strategy. This is cross-functional.
Waiting for “Perfect Standards”
Waiting for complete certainty delays preparation unnecessarily. Preparation can begin before every standard fully stabilizes.
Ignoring Legacy Systems
Old systems are often hardest to migrate. And usually most vulnerable.
Focusing Only on New Applications
Many organizations modernize new builds while ignoring existing risk. That creates a false sense of progress.
Read More: What is Neuro-Symbolic AI? The Future of Reliable Machine Reasoning
Enterprise Readiness Framework
Readiness Level |
Characteristics |
Risk Position |
| Reactive | No inventory, no planning | High Risk |
| Aware | Leadership informed, limited discovery | Moderate-High Risk |
| Preparing | Inventory underway, roadmap forming | Moderate Risk |
| Executing | Migration phased and active | Lower Risk |
| Agile | Governance and crypto-agility mature | Strong Position |
Why This Matters for Enterprise Product Teams Too
Quantum-readiness is not only infrastructure-related. It impacts product architecture.
Future-facing:
- Enterprise app development strategies
- Authentication platform design
- API infrastructure
- Customer-facing security models
- Internal tooling frameworks
Any organization building long-lifecycle software today should already account for future cryptographic adaptability. Otherwise, you are building tomorrow’s migration burden into today’s product.
If Your Encryption Strategy Assumes Quantum Can Wait, You Are Already Behind
Most businesses will not lose because quantum computing arrived unexpectedly. They will lose because they assumed preparation could start later. If your organization stores sensitive long-term data, runs legacy encryption infrastructure, or depends heavily on older enterprise systems, your migration window may already be shorter than you think.
The smartest organizations are not waiting for panic. They are building transition plans now while they still have time to do it properly. If your business is evaluating modernization, infrastructure security, or future-proof digital architecture, now is the right time to begin serious Post-Quantum Cryptography planning before urgency replaces strategy.
Final Thoughts
Quantum disruption is still approaching gradually. But cryptographic migration at enterprise scale never happens quickly. That is the part many organizations underestimate. By the time quantum threats become immediate, businesses without preparation will be forced into rushed, expensive, reactive security overhauls. That is rarely where good decisions happen.
Post-Quantum Cryptography migration is not about panic. It is about recognizing that infrastructure decisions made today determine whether your organization is secure tomorrow. And in security, the best time to prepare is usually before everyone agrees it is urgent.











